
It's nice to start a day with a walk through a park...
My thought order will be kinda chaotic in this post :)
One of the advantages of working with Hispasec was the diversity of things to do. So, I've reversed malware, written software in Java, done pentests, written scripts in Python/BAT, created tools and apps in C/C++, written in PHP, done some vulnerability research in software, and even done some minor forensics. At some point, when we created a Polish lab for Hispasec, I even got to work as a kind of management person (it's not easy work my friends ;>).
Actually, I've made a mistake in the above sentences. I've used a singular form, where I should have used a plural, since most of the projects were done in teams, especially when other Poles started to join the company (morel, Icewall, j00ru, pi3) :)

Confidence 2008 - the first security conference I've attended; a photo with the conference and Capture The Flag staff after team Hispasec won both the Wargame and CTF :)
Another pro was the conference I could finally take part in (thanks to a little financial help from my boss) - it began with Confidence 2008 - the first security conference I've attended. It was great, since, besides me, also some other Hispasec people got there - Icewall, morel from Poland, and also Emi and Julio from the Malaga division. Using our combined strengths we've managed to win both the Wargame challenge and the Capture The Flag competition (I really enjoy security challenges ;>). Hehe, well, actually team Hispasec has won most of the competitions on the future editions of CONFidence too - the CTF and ESET CrackMe in 2009 and the ESET CrackMe in 2010 (the CTF in 2010 did not take place ;<).

SysDay 2009, the Hispasec logo placed once again in my slides :)
After the CONFidence 2008 I've attended also Sekit 2008 (as a speaker; I've met pi3 there, he had joined Hispasec few months later, and later left for CERN in Switzerland), IT Underground 2008 (participant), SysDay 2009 (Hispasec had two speakers there - pi3 (streamed live) and mine), SEConference 2009 (as a speaker), CONFidence 2009 (participant), SecDay 2009 (three Hispasec speakers this time - Icewall has talked about bankers, j00ru about a bootkit he developed, and me about PHP Internals), CONFidence 2.0 (as a speaker), Hack In The Box 2010 (remotely, as a speaker; some Island volcano has canceled my flights, and I had to do the talk via a phone + video streaming of my desktop ;>), CONFidence 2010 (with j00ru we talked about the vulnerabilities in Windows that we've found), and a few days ago I've mentioned that I'm working with Hispasec for the last time, at RECON 2010 in Montreal, Canada.
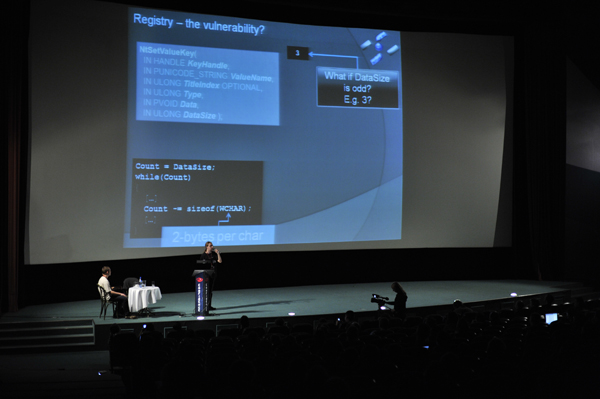
Confidence 2010 - two years after my first Confidence; a lecture with j00ru, and the Hispasec logo in the corner of each slide ;)
Hispasec is the place where I started to play with vulnerability research (aka bughunt), what resulted in found, reported and disclosed bugs in, inter alia, Total Commander, SDL_Image (huh, I didn't know a guy from Blizzard is working on it), Mozilla Firefox, Opera, Apple Safari (actually it was bug in an image handling library in OSX), StarCraft, and (together with j00ru) in Windows (seven vulnerabilities).
Also, I was able to publish some research, e.g. in 5 articles for Hakin9 (in Polish), 3 for Xploit (also in Polish), one for HITB Magazine, many as posts on my blog, and one as an independent PDF posted on the web (with j00ru, "GDT and LDT in Windows kernel vulnerability exploitation").
Well, it was a pretty busy period :)
I've learned many things about malware too. How do they work from a technical point of view (code & netrowk), from the "business" PoV, etc. Sometimes I was like "are you f*cking kidding me?" when I got a 20 MB "Delephant" Delphi trojan to analyse, that used XOR with a 1-byte key for encryption and transmitted the stolen date directly to an SQL database (using libmysql/etc), or even via FTP. Well... ehm.
Sometimes it got more interesting, like for example with Sinowal MBR (aka MEBRoot). During the analysis of this I've learned lots of cool tricks :)

Sevilla in the night, work in the day
As for work mode - most of the time I've worked for Hispasec remotely (the Polish lab was created just last year), meaning no rigid working hours. Hehe, there were a few cases where I've got new "quests", like analysis of a malware sample, at 1 am :) But thats OK, I tend to go to sleep very very... early... in the morning, that is :)
Also, I had a change to visit the beautiful city of Sevilla, ofc due to business stuff :)
When it comes to the people, my co-workers and my bosses, well, I would wish anyone to work with such people :) Countless hours of interesting projects we've done together, hours of interesting discussions, many things I've learned, and ideas I could through and get feedback. The work atmosphere was awesome, kinda loose and very creative :)
As you might have already noticed, I like my work at Hispasec, and I do feel some grief that I'm leaving... But it's time to move on I guess...

New country, new city, new logo for my slides...
From 6th of September I start my work in Zurich, Switzerland. I'll work there on similar stuff, well, maybe except malware analysis. It will be a new country for both me and Arashi, new city, new people to meet and new things to research :) Sounds like fun :)
And I do expect it to be fun. Even during the interviews I had lots of then - the talks were very interesting :)
E.g., during my phone screen with Neel, we were supposed to talk for 30-45 minutes, but we've decided to extend the time, and finally finished after one and a half our - it was very cool, the level of the talk was satisfying indeed, and I've also got to thing about some cool things :)
The Zurich on place interviews were great too... too bad they were time limited ;p
And that's it I guess. Time will tell how will it turn out... but it will turn out good, how else could it turn out, right? ;>
Till the end of August I have a lot of paper work to do due to my relocation, and then there is the relocation itself. Heh, it looks like there is much work to do before the new work may start ;)
P.S. I would like to thank lcamtuf for, well, convincing me to give it a try ;)









Comments:
good luck and have fun :)
Seems so :)
Thanks ;)
Thanks ;) Yeah, Hispasec is great :)
Was great working with you (still is) :)
@fel1x
:) Hi ;)
@Dreg
Thanks Dreg :)
:) thanks mate ;)
@plusvic
Thanks, take care :) It was fun ;)
Good luck with your new proyect.
Hey, thanks mate :)
Yeah, seville was great he he :)
@Julio Canto
Thanks Julio ;) And thanks for recruiting me to Hispasec in the first place too :)))
Yeah, hope the 'little' company will be as much fun as Hispasec :)))
Yeah, it is a big change huh. Different country, different work style, huh. Good thing they have computers there too ;DDD
Anyway, thanks ;) I hope I'll be able to attend IGK anyway ;)
Add a comment: